Aes Key Generation Python Code
Released:
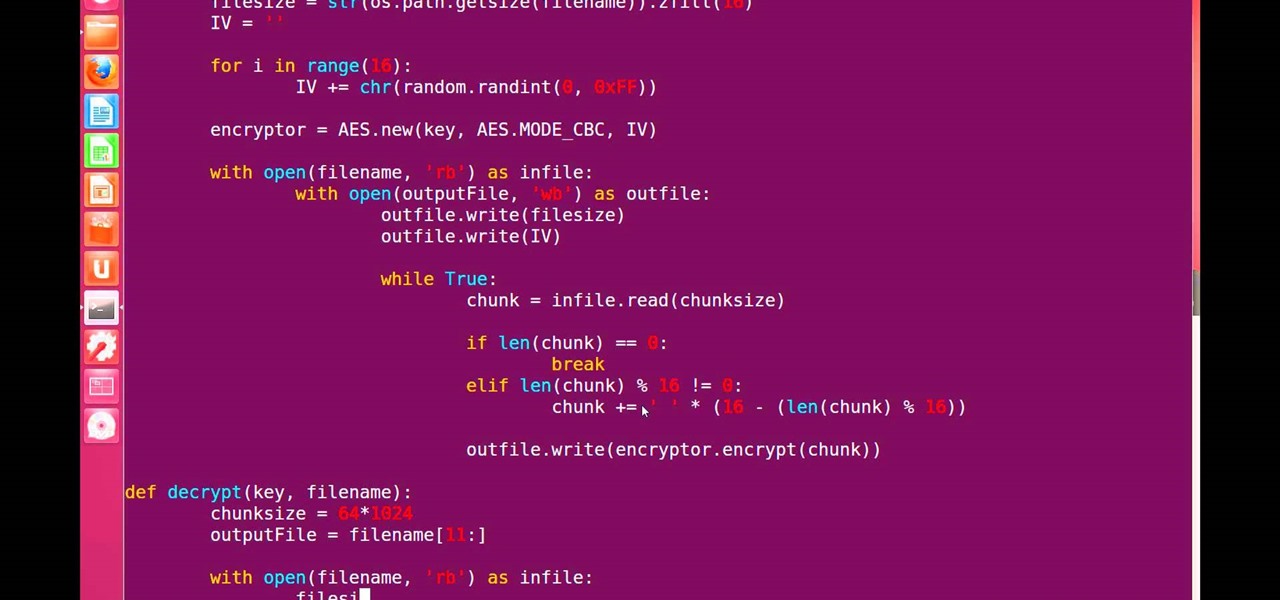
Sep 20, 2017 Supports all AES key sizes; Supports all AES common modes; Pure-Python (no external dependencies) BlockFeeder API allows streams to easily be encrypted and decrypted; Python 2.x and 3.x support (make sure you pass in bytes, not strings for Python 3) API. All keys may be 128 bits (16 bytes), 192 bits (24 bytes) or 256 bits (32 bytes) long. Pip3 install pycrypto. In the following python 3 program, we use pycrypto classes for AES 256 encryption and decryption. The program asks the user for a password (passphrase) for encrypting the data. This passphrase is converted to a hash value before using it as the key for encryption. Sep 08, 2014 The given master key is stretched and expanded by PKBDF2-HMAC(SHA256) using the salt from 1), to generate the AES key, HMAC key and IV (initialization vector for CBC). The given message is encrypted with AES-128 using the AES key and IV from step 2), in CBC mode and PKCS#7 padding.
Pycrypto based Simple And Easy Cipher on AES Lgd415 msl code free download.
Project description
Pycrypto based Simple And Easy AES Cipher
Dependencies

- Python 2.7 or later
- Pycrypto 2.6.1 or later
Usage
Project details
Release historyRelease notifications
1.0.7
1.0.6
Download files
Aes Key Generation Python Code Online
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
| Filename, size | File type | Python version | Upload date | Hashes |
|---|---|---|---|---|
| Filename, size Simple-AES-Cipher-1.0.7.tar.gz (2.7 kB) | File type Source | Python version None | Upload date | Hashes |
Hashes for Simple-AES-Cipher-1.0.7.tar.gz
| Algorithm | Hash digest |
|---|---|
| SHA256 | ba83df87ff16bed219f6d4d2eb6aa9d961ec81a6a3c6fdf2b152c9d9ee270ef7 |
| MD5 | a45a617a918f8ef616ea0782bdf17765 |
| BLAKE2-256 | 6b6f29d1e26e47cd775870534a1600d6fb9187b5ebaa4e401623b6203c676b57 |
This is an exercise in secure symmetric-key encryption, implemented in purePython (only built-in libraries used), expanded from Bo Zhu's (http://about.bozhu.me)AES-128 implementation at https://github.com/bozhu/AES-Python
- AES-128, AES-192 and AES-256 implementations in pure python (very slow, butworks).Results have been tested against the NIST standard (http://csrc.nist.gov/publications/fips/fips197/fips-197.pdf)
- CBC mode for AES with PKCS#7 padding (now also PCBC, CFB, OFB and CTR thanks to @righthandabacus!)
encryptanddecryptfunctions for protecting arbitrary data with apassword
Aes Key Generation Python Code Download
Note: this implementation is not resistant to side channel attacks.
Although this is an exercise, the encrypt and decrypt functions shouldprovide reasonable security to encrypted messages. It ensures the data iskept secret (using AES), blocks are encrypted together (CBC), the samemessage encrypted twice will have different ciphertexts (salt), the ciphertexthasn't been tampered with (HMAC) and the key has some defense against brute-force(PBKDF2).
The algorithm is as follows:
16 random bytes of salt are extracted from the system's secure random numbergenerator (usually /dev/urandom)>
The given master key is stretched and expanded by PKBDF2-HMAC(SHA256) usingthe salt from 1), to generate the AES key, HMAC key and IV (initializationvector for CBC).
The given message is encrypted with AES-128 using the AES key and IV fromstep 2), in CBC mode and PKCS#7 padding.
A HMAC-SHA256 is generated from the concatenation of the salt from 1) andthe ciphertext from 3).
The final ciphertext is HMAC + salt + ciphertext.
Security overview:
Aes Python Crypto
The random salt ensures the same message will map to different ciphertexts.
The HMAC ensures the integrity of both the entire ciphertext and the PKBDF2salt; encrypt-then-mac prevents attacks like Padding Oracle.
Bytes from keys, iv and salt are not reused in different algorithms.
PBKDF2 key stretching allows for relatively weak passwords to be used as AESkeys and be moderately resistant to brute-force, but sacrificing performance.