Generate Random Aes Key Online
Key generators are constructed using one of the getInstance class methods of this class.
- GETAKEY.ONLINE - Encryption Key Generator. Machine Key Generator. WPA Key Generator. WEP Key Generator. Data we generate for you is never kept on our servers.
- Jan 16, 2009 I came across the Ultra High Security Password Generator the other day, which uses a very high quality pseudo-random number generator to generate passwords and keys. The idea is not to use the full 63 characters as a password, but rather a contiguous subset, such as the first 8 characters.
KeyGenerator objects are reusable, i.e., after a key has been generated, the same KeyGenerator object can be re-used to generate further keys.
This class provides the functionality of a secret (symmetric) key generator. Key generators are constructed using one of the getInstance class methods of this class. KeyGenerator objects are reusable, i.e., after a key has been generated, the same KeyGenerator object can be re-used to generate further keys.
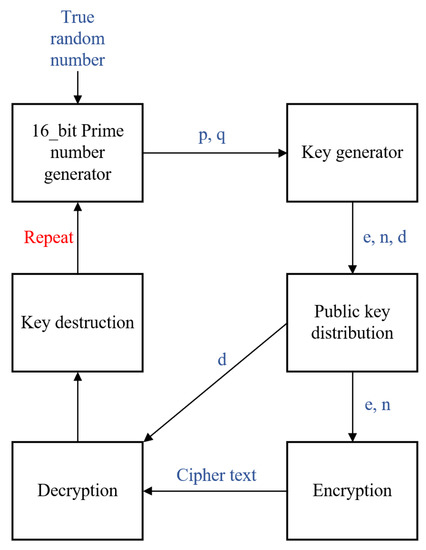
There are two ways to generate a key: in an algorithm-independent manner, and in an algorithm-specific manner. The only difference between the two is the initialization of the object:
- Algorithm-Independent Initialization
All key generators share the concepts of a keysize and a source of randomness. There is an
initmethod in this KeyGenerator class that takes these two universally shared types of arguments. Free avs video editor 8.0.3.303 full serial key. There is also one that takes just akeysizeargument, and uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation), and one that takes just a source of randomness.Since no other parameters are specified when you call the above algorithm-independent
initmethods, it is up to the provider what to do about the algorithm-specific parameters (if any) to be associated with each of the keys. - Algorithm-Specific Initialization
For situations where a set of algorithm-specific parameters already exists, there are two
initmethods that have anAlgorithmParameterSpecargument. One also has aSecureRandomargument, while the other uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation).
In case the client does not explicitly initialize the KeyGenerator (via a call to an init method), each provider must supply (and document) a default initialization.
Every implementation of the Java platform is required to support the following standard KeyGenerator algorithms with the keysizes in parentheses:
- AES (128)
- DES (56)
- DESede (168)
- HmacSHA1
- HmacSHA256
There are multiple ways of generating an encryption key. Windows 7 professional service pack 1 key generator. Most implementations rely on a random object. All examples mentioned here use a secure cryptographic randomizer.
PowerShell
Base64
Hex
C#
The code snippets below can be run from LINQPad or by copying the following code into a new project and referencing System.Security.
Base64
Hex
OpenSSL
OpenSSL is well known for its ability to generate certificates but it can also be used to generate random data.
Base64
Generates 32 random bytes (256bits) in a base64 encoded output:
Generate Random Aes Key Online Banking
Plaintext
Aes Key Fortnite
Generates 32 random characters (256bits): Lcg jukebox unlock key generator.
Related Articles
Aes Key Absent
- Message Property Encryption
Encrypt message fragments using property encryption. - Security
Security features for messages, transports, and persisters.